Hackers, or those who endeavour to breach data networks that belong to others, are often smart people. For any data network, security is an issue. No system should be left unprotected and unscrupulous people will always exist who want to take advantage of an unprotected system. In general terms, VoIP systems are relatively secure, but should some determined hacker target your network, then there are a few useful things to know to keep them at bay.
Be prepared
VoIP suppliers today know that the major challenges facing this technology are delivering a reliable service of consistent quality. However, a security strategy is an essential investment. Hacking is one possibility, but VoIP attacks could also take the form of an interruption to service, or Denial of Service, known as a DOS.
VoIP can also be subject to spam, just as an email account can be. VoIP spam is called SPIT, or Spam over Internet Telephony. This is probably more aggravation than consternation, but you could come into work to find 20 messages about winning a free trip to Nigeria and somehow all the charges have accrued to you.
Eavesdropping is another potential issue, where unwanted listeners are invading the privacy of your communications. This phenomenon is rather amusingly called VOMIT, or Voice Over Misconfigured Internet Telephony. Needless to say, SPIT and VOMIT are to be avoided.
Not all VoIP systems are the same
VoIP systems can vary a great deal and this means that the security issues affecting them can vary too. As a VoIP system can be customised, security protection systems can be developed to guard the most sensitive elements of the system. For example, staff can have individual VoIP logins that allow access to certain areas of the system only, with the most sensitive data requiring a higher level of access and a more sophisticated method of logging in to this area.
There are two broad categories of VoIP service, the managed service via an IP Centrex, and the IP-PBX based solution. The IP-PBX system can operate in a similar way to a traditional PBX system using a private connection, but with IP. Both types of system have advantages and disadvantages. The more private the infrastructure, the safer it will be. When elements of public systems are added, then opportunities for breaches could be introduced. Security options associated with any management layers need to be assessed as well.
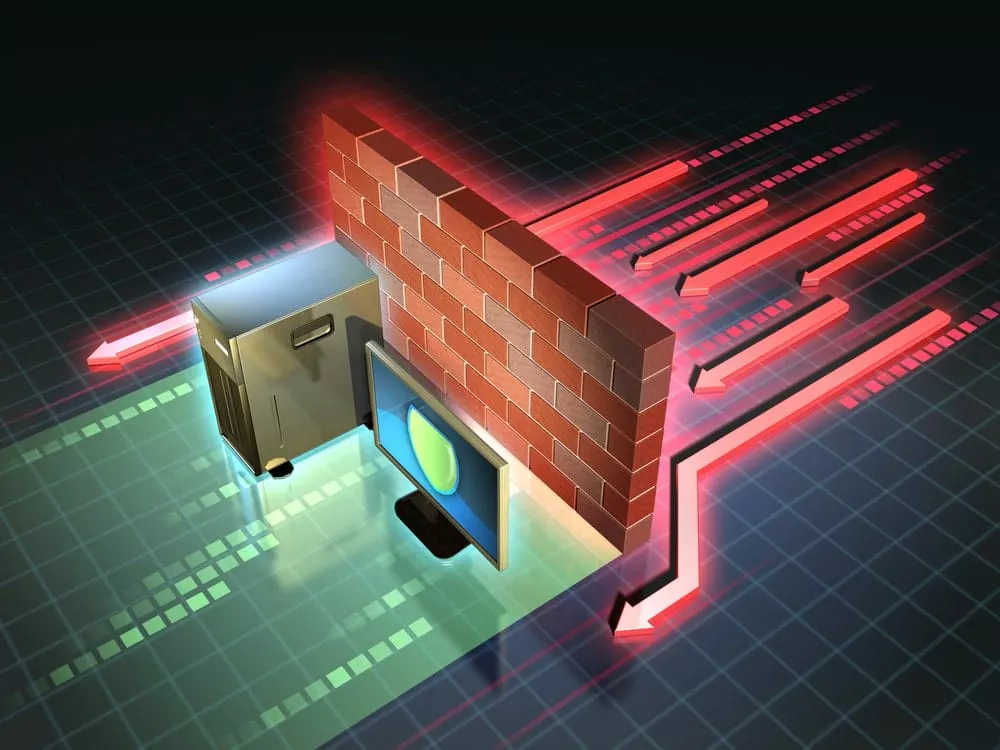
More than a firewall
Many companies make the error of thinking that if they have a firewall and a VPN – or Virtual Private Network – tunnel, then that’s all they need. A VPN tunnel can support encryption and authentication, but their efficacy depends on the strength of the firewall. If the firewall is compromised, then so may be the VPN tunnel.
The use of SBCs – or Session Border Controllers – is increasing, as they can direct telephony through the business’ own network, separating data from voice and treating each as a separate entity. SBCs can create a one-time channel – or pinhole – for a particular event or session, so when that has concluded, the pinhole is closed with no opportunity to breach or use it as a way of gaining access to the rest of the network. SBCs are suitable for use with private VoIP services.
Voicemail can present a vulnerability to hackers. However, voicemail can be managed in ways that allow staff to obtain voicemail, without then remaining in the system or providing a way for hackers to gain access.
Advantages of a VoIP wholesale carrier
If you are running a business and looking for a way to maximise value from your communications system, then it makes sense to find a VoIP wholesale carrier that offers competitive rates. A long-established carrier such as IDT will be able to offer an extensive global network of providers throughout the world, so no matter where or who you are calling on your VoIP system, you will benefit from the best and lowest rates.
Termination rates, particularly for a firm which does a lot of international business or which has staff who travel frequently, are one area where VoIP costs can vary. If a VoIP call ends at a landline or mobile phone that is connected to a certain provider, then that provider can impose charges. In some developing countries, receiving calls from countries such as the UK is seen as a good way of raising revenues. With a VoIP provider that has a well developed interactional network, this will be less of a problem.
While access and data protection need to be managed, there are so many significant advantages of VoIP that dealing with security should not be a deterrent.
Why not contact IDT today for further help and information.